Building Virtual Labs
Why do some people in information security just seem to pick up new concepts 100x more quickly than others?
It’s not about intelligence. There are tons of smart people who aren’t successful…and tons with average intelligence who become amazingly successful.
It’s also not about time. We all have the same 24 hours in a day.
The secret of leveling up quickly in information security is getting your hands dirty and experimenting.
If you think about professional athletes, you know that they spend most of their time practicing. They practice specific skills and situations in the hope that they are prepared when it is time to perform. Performance is an experience, but practice is a behavior.
What does practice look like for you? It probably involves things like:
- Installing older, vulnerable versions of software and trying to break it
- Capturing packets to learn how services communicate
- Writing IDS signatures to detect malware
- Applying system changes to see how they protect against specific attacks
- Performing attacker activities on systems and reviewing the logs that were generated
- Reverse engineering malware to find out how it works and what it does
In every infosec specialty, practice is facilitated by your security lab. A security lab is the collection of hardware, software, systems, and services that you use to experiment and learn without fear of crashing something important.
Five Reasons Why You Should Build a Security Lab
- Fast-track your career with new skills. Nearly any skill in information security is learnable on your own. The more skills you build, the more appealing you’ll be to hiring managers. There is no quicker way to get hired or promoted than being able to respond to a question with “I know, I just tried that in my lab last night.”
- Become a doer instead of a talker. Most experienced practitioners can discern the voice of someone who has only read about something versus someone who has actually done it. Putting hands-on-keyboard is critical to gaining mastery over concepts you’ll need to be successful, and a lab environment is a safe and convenient way to do it.
- Find your passion and spark your curiosity. Within all of us, we have a beast called curiosity, and it needs to be fed to grow. When you experiment in a lab, you’ll inevitably find things that pique your interest and push you to dig deeper. Not only are you learning, you cultivate your desire to learn.
- Learn how to perform attacks. You can setup intentionally vulnerable systems in your lab and test different ways to break into them. You can also practice lateral movements techniques leveraging built-in tools. This will help you understand the skills needed to become a penetration tester.
- Learn how to catch bad guys. If you pair your attack simulation with intrusion monitoring and detection tools, you’ll be well positioned to learn how to detect and prevent those attacks using host and network data. This will help you understand the skills needed to become a security analyst or incident responder.
There are plenty of articles that provide tips on how to build security labs, but I want to do something better. Instead of telling you how to build a security lab, I’m going to show you.
Introducing…
If you’re an information technology or security practitioner who wants to learn more about your craft, then this is the course that will help you build your own lab for practicing and learning technology skills.Building Virtual Labs is a hands-on “choose your own adventure” style walkthrough for building an IT security lab for penetration testing, network security monitoring, and more.
Building Virtual Labs is for you if:
- You want to enhance your IT or security skills by getting hands-on practice attacking and defending systems
- You’ve always wanted to build a lab but never knew where to start
- You’re overwhelmed by all the configuration details that go into building a lab and want a complete guide on the entire process from A to Z
- You don’t know how to configure virtual networking so that systems can talk to each other securely
- You want to learn what types of systems should be contained in a virtual lab
- You want to break into information security and gain the skills necessary to land your first job on the red or blue team
- You’ve started to build your lab a few times, but progress just stalled
Building Virtual Labs will show you every step needed to build a robust lab for experimenting with and learning about network attack and defense.
Course Format
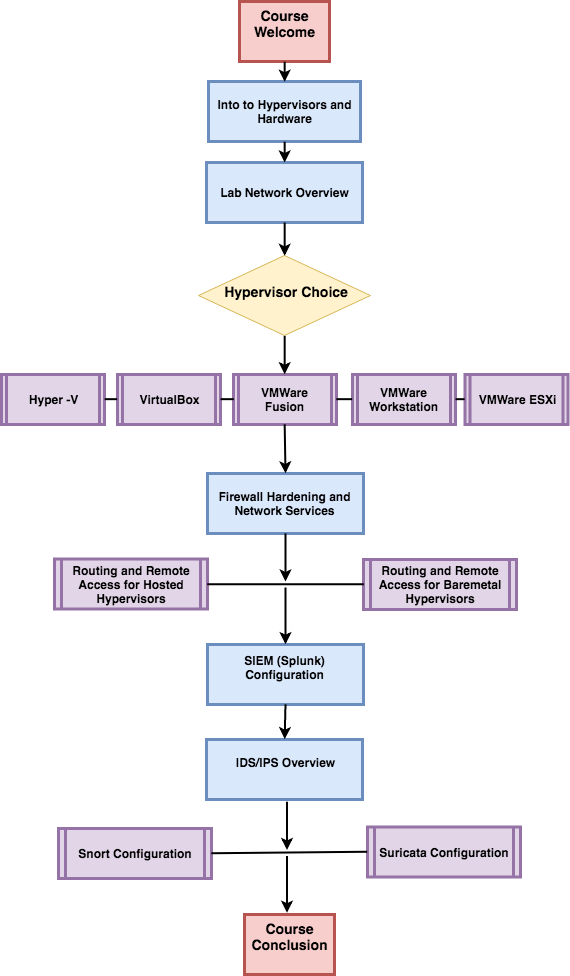
Building Virtual Labs is built as a “choose your own adventure” style course. You’ll begin with an overview of the lab architecture and important considerations for any virtual lab. After that, you’ll be presented with some options for the hypervisor platform for the lab, and you’ll go through the video tutorial for setting it up and deploying your virtual machines. We’ll show you how to configuring routing and remote access, set up your firewall and harden network services, and how to take good notes so you can keep track of everything. From there, you’ll install and configure several useful services:
- Kali Linux: A penetration testing platform to conduct attacks and simulations
- Metasploitable: An intentionally vulnerable system you can attack
- Snort or Suricata (Your Choice!): An IDS/IPS system to monitor and inspect network traffic.
- Splunk: A SIEM/Log Aggregation platform to receive IDS alerts and any other log data you want to ingest.
The course is delivered on-demand so you can proceed through it at your convenience.
Although the course is recorded, you’ll have direct access to the instructor in case you get stuck or have questions about unique ways to use your lab.
You can view the full course syllabus here.
Building Virtual Labs includes:
- Over 20 hours of demonstration videos. These videos will show you every concrete step needed to build your own lab.
- One on one instructor access. Run into problems with a step? Want to know how to extend one of the concepts for your own needs? No problem. You can ask questions directly to the instructor within the course.
- Continuing education credits (CPEs/CMUs). Once you’ve completed the course you’ll receive a certificate you can use to claim credits for various certification maintenance programs like the CISSP or GIAC certifications.
- Participation in our student charitable profit sharing program.A few times a year we designate a portion of our proceeds for charitable causes. AND students get to take part in nominating charities that are important to them to receive these donations.
- 1-year access to course video lectures and lab exercises. You can extend access later if you need more time.
- A Certification of Completion
- 20 Continuing Education Credits (CPEs/CEUs)
Frequently Asked Questions:
Is this course live?
This is NOT a live course. It’s an online video course you can take at your own pace.
How long do I have access to the course material?
You have access to the course for one year following your purchase date.
How much time does it take to do this course?
Because this is a “choose your own adventure” style course, the estimated time to complete it is highly variable. If you go through every course video for a single hypervisor, you can expect to view around 12 hours of video content.
How many CPEs/CMUs is this course worth?
Organizations calculate continuing education credits in different ways, but they are often based on the length of the training. This course averages 20 hours of video+lab work.
Student Testimonials
“If someone is trying to get into InfoSec or even just IT in general, I would recommend they take this course. I recently transitioned out of the military in search of employment in an IT field. I am now able to discuss during interviews, some details about my home lab such as how it works, what it is and can be used for, and what I have learned from it. Thank you to Tony for the passion it took to write the book and record the video. I admire his sincerity and drive to help others learn and for providing the platform to get started” – G. Sena
Join Building Virtual Labs Now for Just $197
Bulk discounts are available for organizations that want to purchase multiple licenses for this virtual lab training course. Please contact us to discuss payment and pricing.