YARA for Security Analysts
Learn to use YARA to detect malware, triage compromised systems, and perform threat intelligence research.
Detecting malicious elements within files is a core security skill for incident responders, SOC analysts, threat intelligence analysts, malware analysts, and detection engineers alike. There are different ways to accomplish that goal, but none are more flexible or widely used as YARA.
YARA is a pattern-matching tool used to help identify and classify malware in a variety of scenarios. By writing YARA rules, security practitioners can detect whether malware exists within a group of files, triage a potentially compromised host, or identify common elements between samples to bolster threat intelligence.
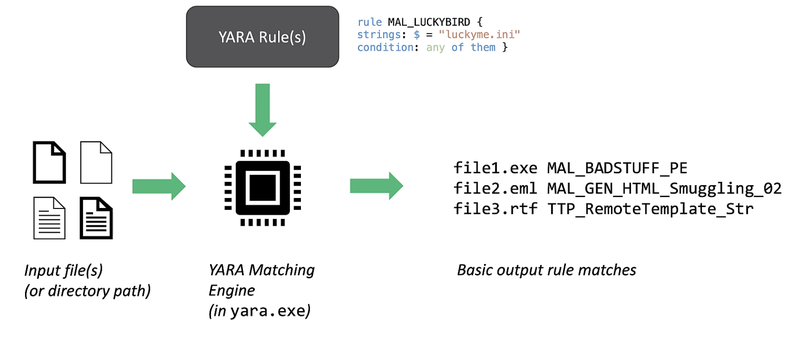
The YARA syntax provides a simple and powerful framework for expressing detection logic for file content. Using the YARA executable, you can search for matches based on the rules you write across a single folder or entire system. When you write detection rules for YARA, you can apply those rules in a variety of scenarios and share the rules with your peers in the detection and threat intel communities.
“Most security practitioners should be familiar with the holy trinity of detection. That’s Suricata for network traffic, Sigma for logs, and YARA for files.”
YARA is the open-source standard for detecting malicious file-based content, but there has never been a course that takes a foundational approach to learning detection engineering through the lens of YARA…. until now.
I’m excited to offer an online course that will teach you how to interpret, build, and tune YARA rules to become a better detection engineer or analyst.
Introducing…

YARA for Security Analysts will teach you how to write, tune, and leverage YARA rules to aid security investigations and research. This course requires no prior YARA experience and will take you from beginner rule writing through advanced techniques.
You'll learn...
YARA Fundamentals
- The anatomy of YARA rules
- Rule composition and sequencing
- Rule testing at the command line and with CyberChef
YARA Rule Syntax
- String matching basics
- Matching hexadecimal values
- Complex matches with regular expressions
- Controlling matches with rule conditions
- Using modules to extend YARA functionality
Detection Research Methodology
- The detection research process from the ground up
- How to build and manage a malware corpus
- Common file formats and how to approach them
- Bulk rule testing against malware corpora
- Detection based on exported functions and code-signing certificates
Ruleset Management
- Building global vs. private rules
- Tuning false positives
- Resources for performance measurement and tuning
Adversary Tradecraft
- Common “generic” detection ideas for hunting
- Identifying malware masquerades
- Finding high entropy content
- Identifying the use of linked libraries
- How attackers leverage stack strings
- Detecting obfuscated strings
Extended Topics
- Content ordering and proximity
- Writing rules for features that modules don’t identify
- Bulk rule creation with CyberChef and text editors
- Accelerating rule writing with scripts
- Using external variables
You’ll start by learning the common use cases for YARA and the basic structure of its rules. We’ll walk through several examples where I show you how to write simple rules for real malware, and you’ll get some practice interpreting and fixing pre-written rules. As we progress, you’ll work through labs where you’ll write your own rules based on malware samples that I provide. In most cases, I’ll provide a video walkthrough demonstrating how I approached writing the lab rules, but you should save those for after you’ve made your own attempt.
You’ll quickly become comfortable writing YARA rules in the scenarios where they will be most useful for you. I’ll be with you the entire way to provide feedback on your work and push you forward.
If you want to learn how to write efficient and effective YARA rules for detection, response, or threat intelligence… YARA for Security Analysts is the course you’re looking for.
You can view a detailed course syllabus here and a sample video here.
YARA for Security Analysts Includes:
Over 20 hours of demonstration videos. These videos will break down the concepts and skills you need to become adept at writing YARA rules to detect diverse malware characteristics.
Hands-on labs to help you develop and test your skills. You’ll complete lab exercises by following along with class demonstrations and analyzing real malware to write your own YARA rules. I’ll be with you along the way to provide guidance and feedback on your work.
Participation in our student charitable profit-sharing program. A few times a year we designate a portion of our proceeds for charitable causes. AND students get to take part in nominating charities that are important to them to receive these donations.
Frequently Asked Questions
Is this course live?
This is NOT a live course. It’s an online video course you can take at your own pace. You’ll interact with the instructor asynchronous through the course exercises.
How long do I have access to the course material?
You have access to the course for six months following your purchase date. If you need more time, you can extend your access for a small monthly fee.
Are there any prerequisites or lab requirements for this course?
This course is designed for all security practitioner skill levels and assumes no prior YARA experience. You should have some basic knowledge of malware to include safe handling, dumping file strings, and opening malware in hex editor to examine byte content. To follow along with the labs and lab solutions, you should have some familiarity with Linux commands such as awk, uniq, and sort (though all the labs can be completed on any platform).
Because you’ll be working with live malware samples, we typically recommend a virtual system that you can disconnect from the Internet and revert back to a snapshot as needed.
Though this is not mandatory for the course, to best enable testing YARA rules on large malware and goodware sample sets, we recommend at least 8GB of RAM and at least 100GB of disk space.
How much time does it take to do this course?
Given the number of lab exercises, completing the course takes people varying times. You can plan for around 20 hours of lecture and demonstration lessons and 10-20 hours for lab exercises on your own. We recommend spreading your time in the course out over at least a few weeks to benefit from the effects of spaced learning.
How many CPEs/CMUs is this course worth?
Organizations calculate continuing education credits in different ways, but they are often based on the length of the training. This course averages 30 hours of video+lab work.
Do you offer discounts for groups from the same organization?
Yes. To inquire about discounts or group invoices, please contact us at info@appliednetworkdefense.com.
Meet the Course Author – Steve Miller
Steve Miller is a threat intelligence analyst and researcher of adversary tradecraft, obsessed with finding human fingerprints in digital artifacts. Rather than the What and Why of a breach, he focuses on the Who and the How -- the attribution and modi operandi of cyber threat actors. Steve recently joined Microsoft after eight years at Mandiant working at the intersection of detection, incident response, and threat tracking. Prior to joining Mandiant, Steve did research and special projects for federal government agencies such as the U.S. Department of Homeland Security and the U.S. Department of State. He began his career in security working with the U.S. Army Intelligence and Security Command at the National Security Agency from 2002 to 2008. Steve holds a Bachelor of Science in Computer and Digital Forensics from Champlain College in Vermont. In his spare time, he makes loud spacey noises on modular synthesizers and trains to become an Apex Legend.You can find Steve on LinkedIn or as @stvemillertime on Twitter.
Join YARA for Security Analysts Now for Just $497
Bulk discounts are available for organizations that want to purchase multiple licenses for this YARA training course. Please contact us to discuss payment and pricing.